With Veeam Backup & Replication version 11a, a new Google Cloud Platform (GCP) integration plugin now joins the previously released plugins for AWS and Azure. This plugin allows for integration with the Veeam Backup for GCP appliance, granting management of certain settings through the VBR console and backup copy job support. Configuring this integration is simple.
Pre-Requisites
- Veeam Backup & Replication version 11a or newer is installed
- The following Google APIs are enabled for the project the VMs are hosted under:
- Cloud Deployment Manager V2
- Identity and Access Management (IAM)
- Service Usage
- Google Private Access is enabled for each subnet in use
Appliance Deployment and Configuration
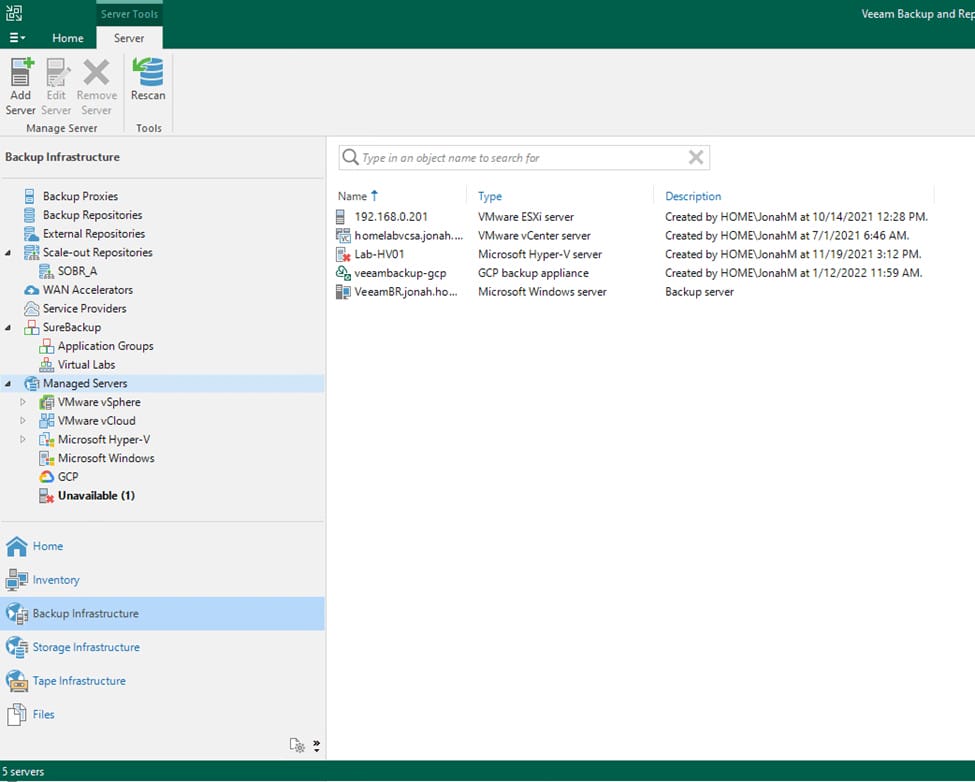
First, let’s begin by launching the Veeam Backup & Replication console and navigating to the Backup Infrastructure view. From here, select Managed Servers from the left-hand menu and click the Add Server button in the top menu.
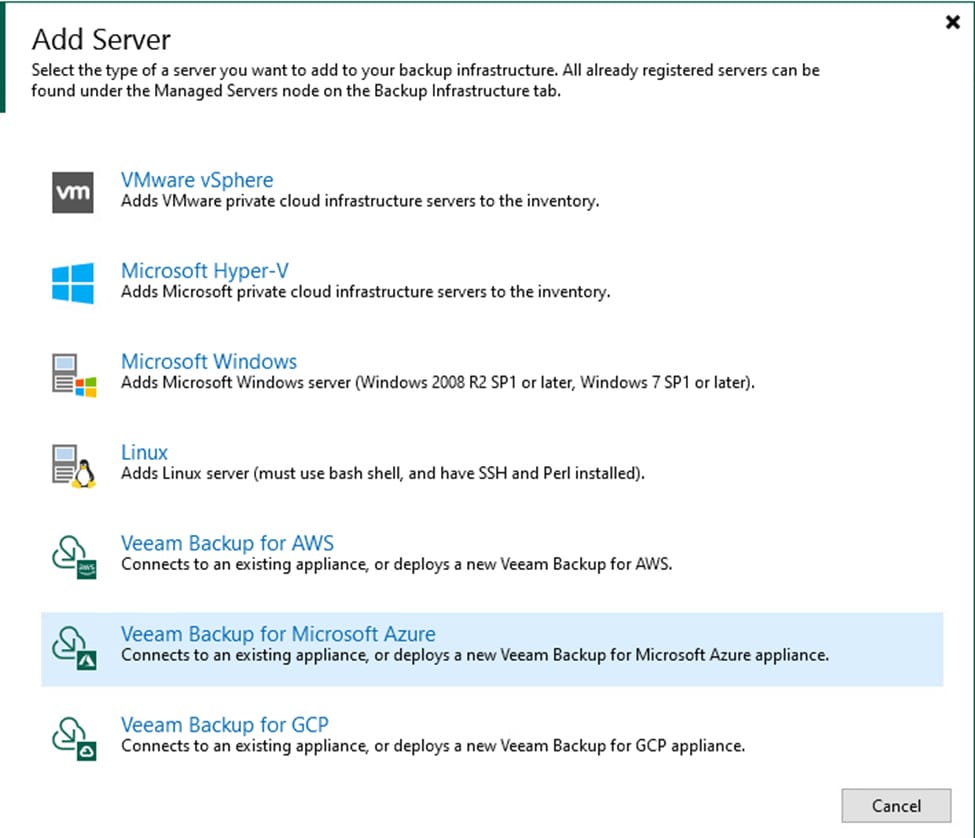
Next, select Veeam Backup for GCP from the available options.
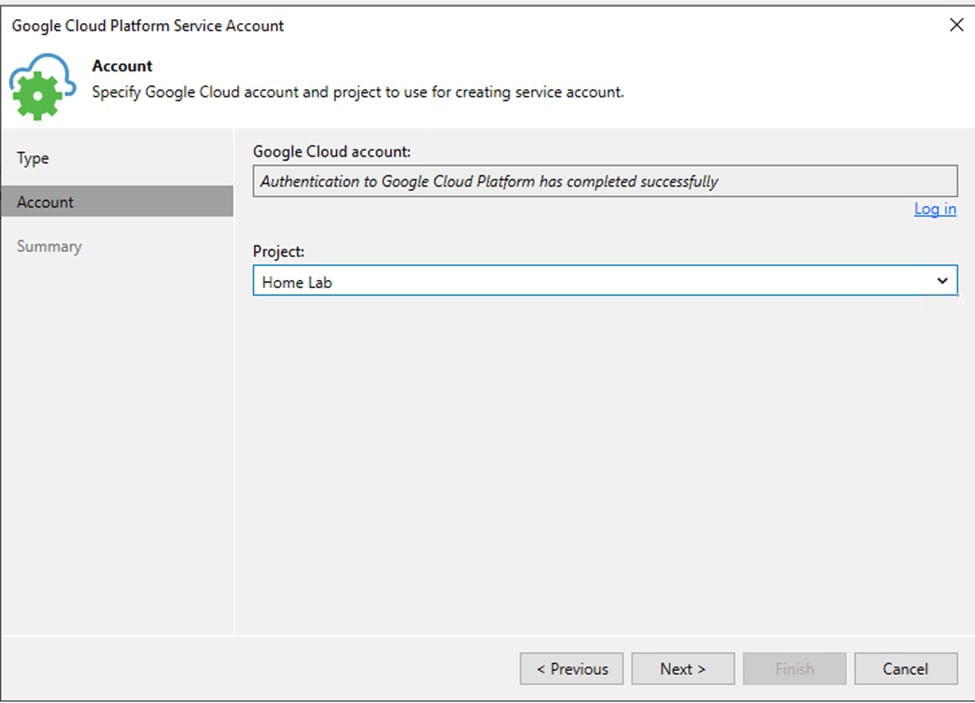
Today, we will be deploying a brand-new backup appliance however, it is also possible to connect to a pre-existing appliance. After selecting the deployment mode, go ahead and add your GCP service account. On this screen, you can either create a new service account (which I have done) or connect to an existing account. Use the Log in hyperlink to connect to your GCP workspace using your Google login, then select the project your workload are located under and proceed to the next screen.
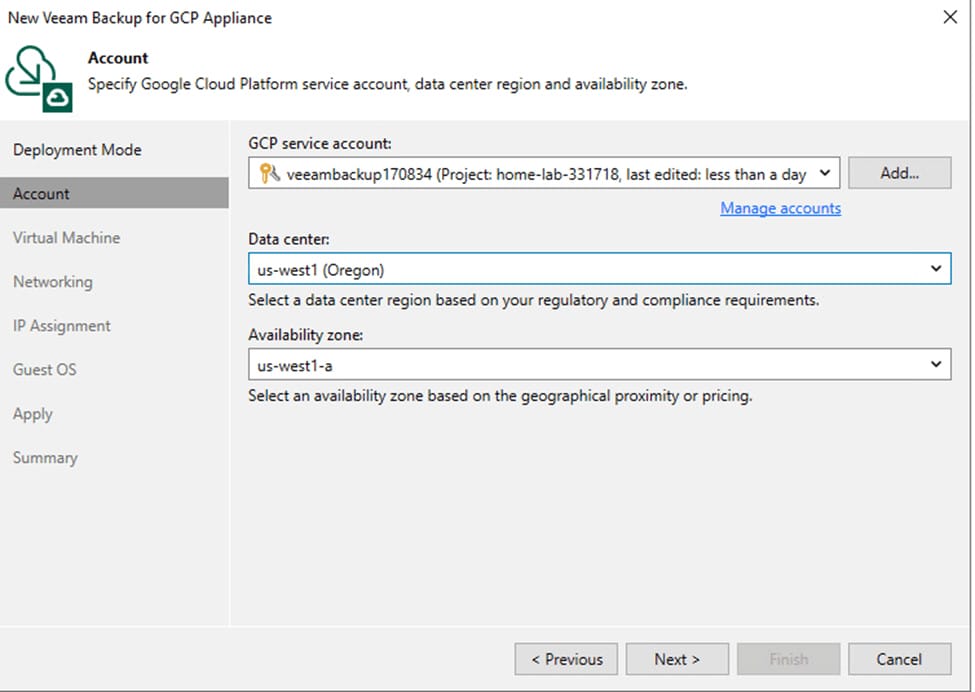
Once the account has been created, click Finish. The GCP service account should populate back in the appliance deployment window, then you should be able to set your data center and availability zone.
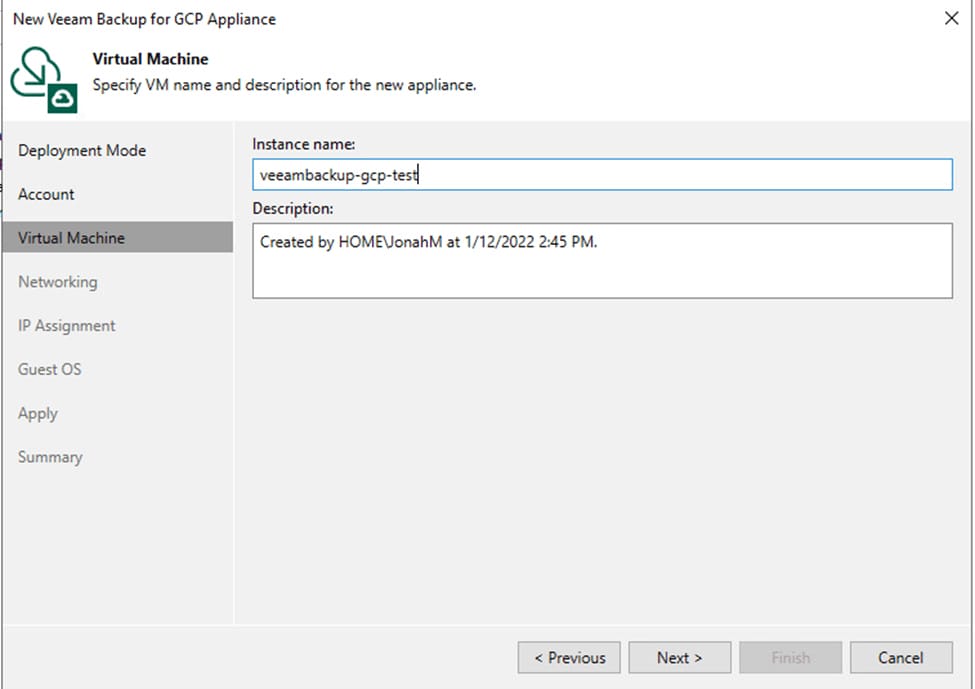
Next, choose an instance name and set a description for the appliance.
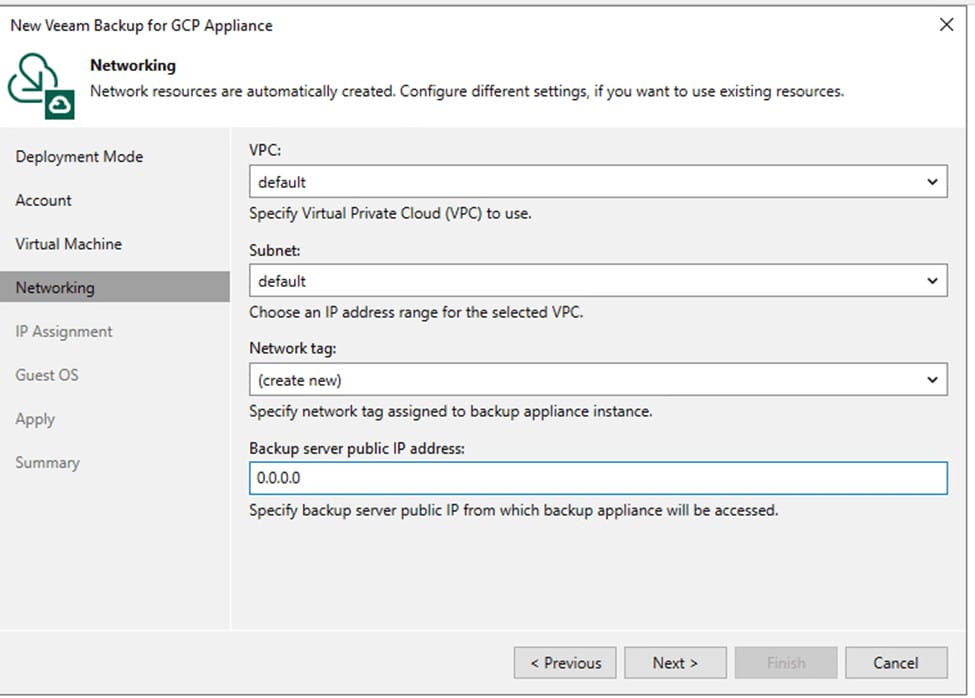
Now network settings are inputted. Here set the VPC, subnet, and network tag. The Backup server public IP address should be pre-populated, but you may need to enter the IP manually.
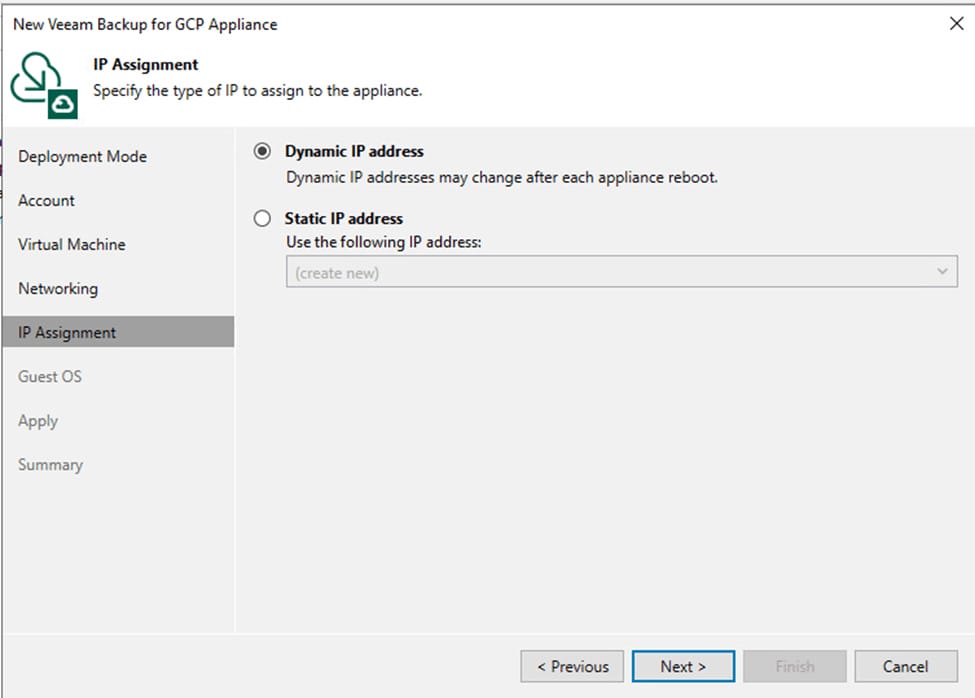
Next, set the IP information. If you have a direct connection between your Veeam server’s location and your GCP environment, set a static IP address here, otherwise leave it set to dynamic so the appliance can be assigned a public address.
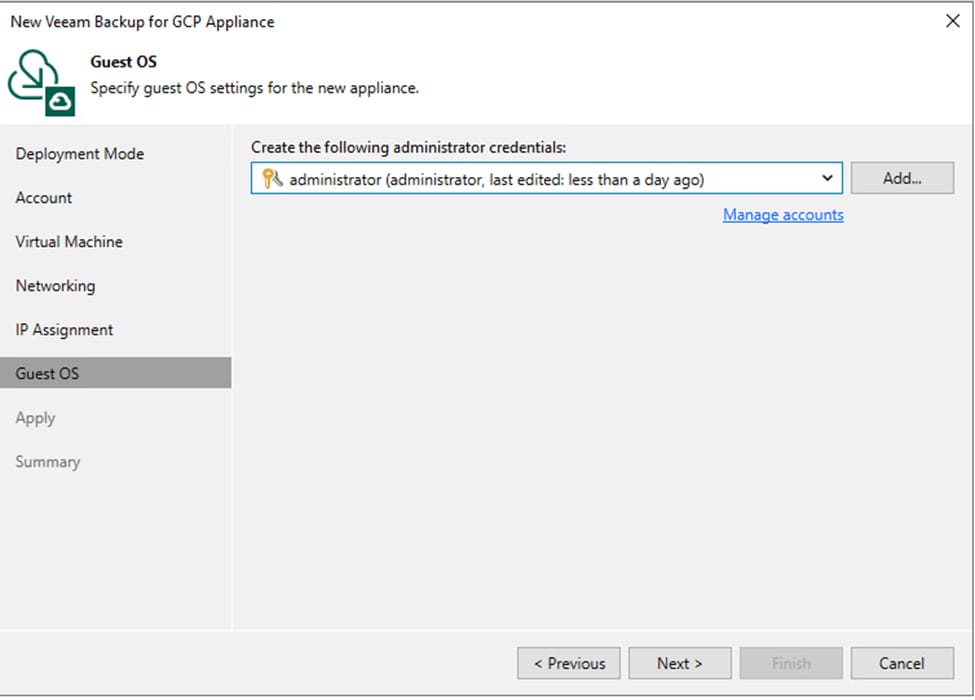
On the next screen, create or choose the administrator credentials you wish to use to log in to the appliance.
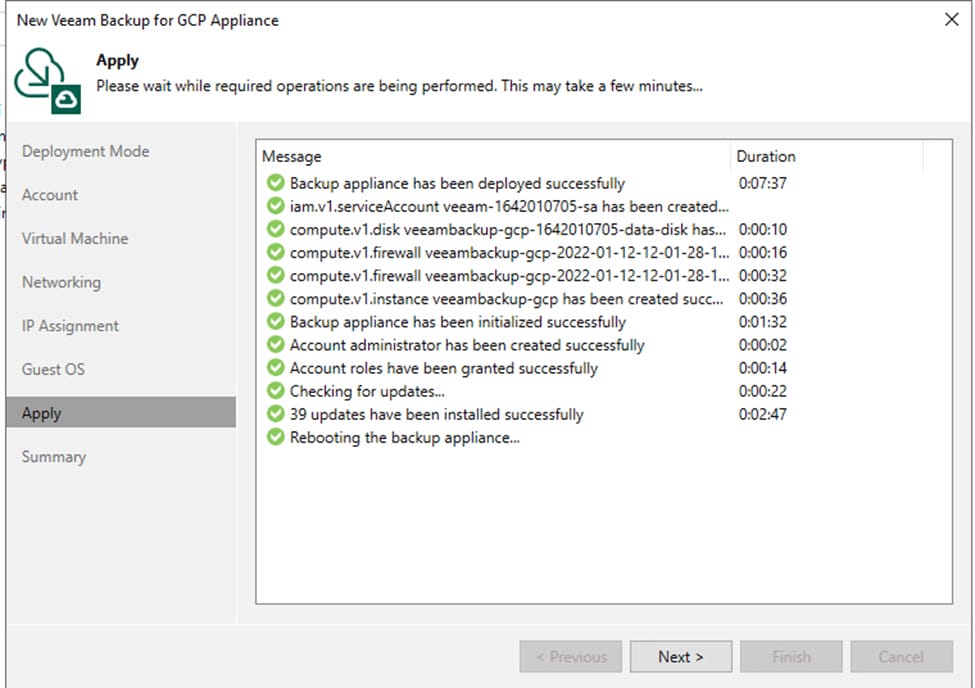
Apply the settings and wait for the appliance deployment to complete. This will take several minutes.
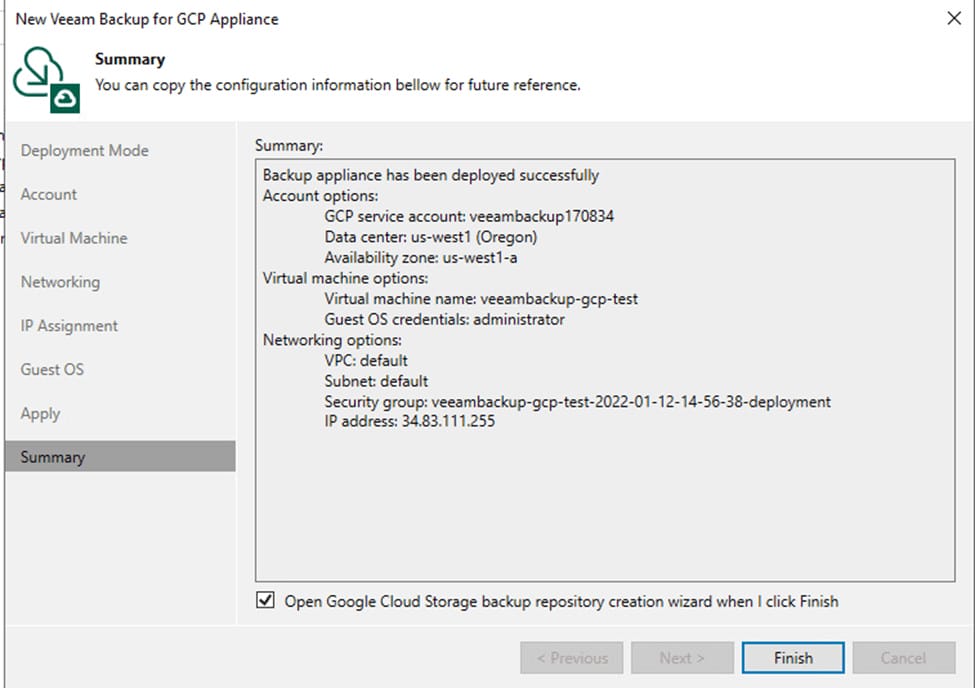
Click Next. Check the box to open the GCS repository creation wizard and click Finish.
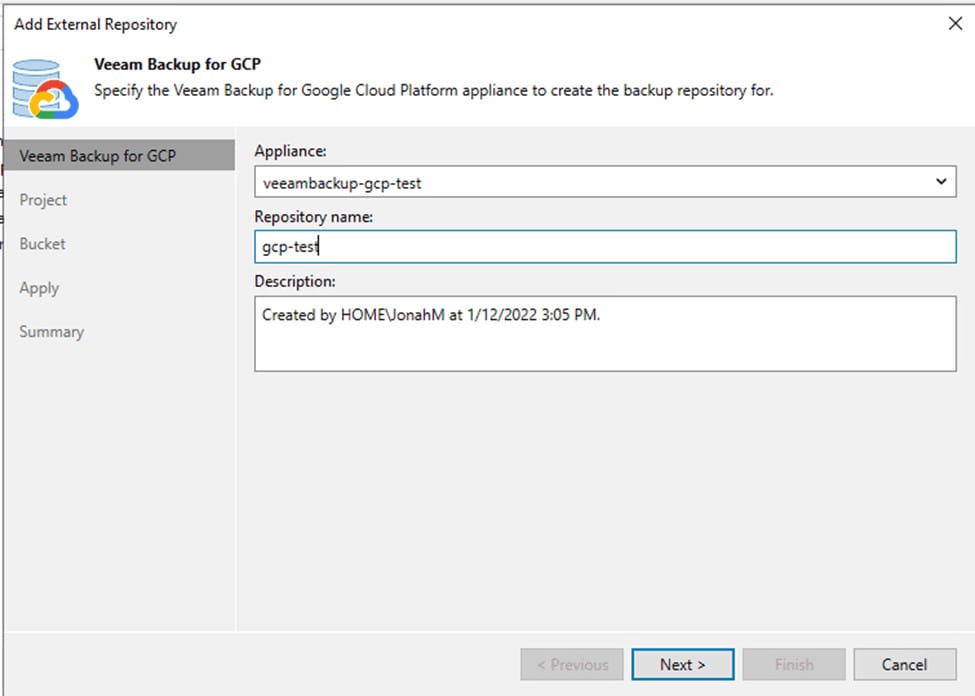
Now, select a repository name and set a description.
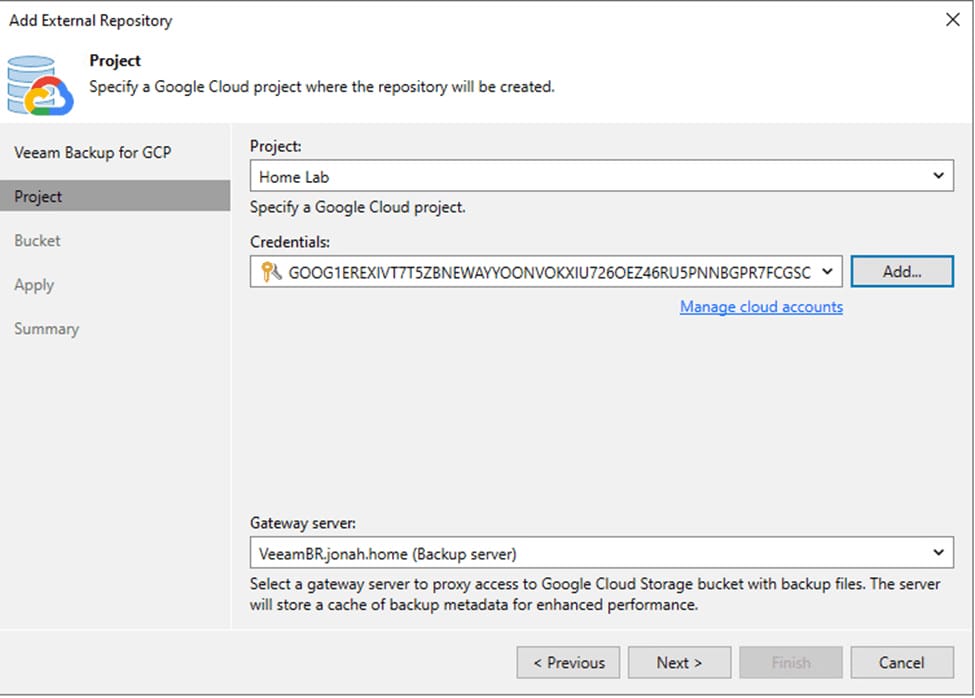
Select the correct project and enter an HMAC key that will be used for bucket access.
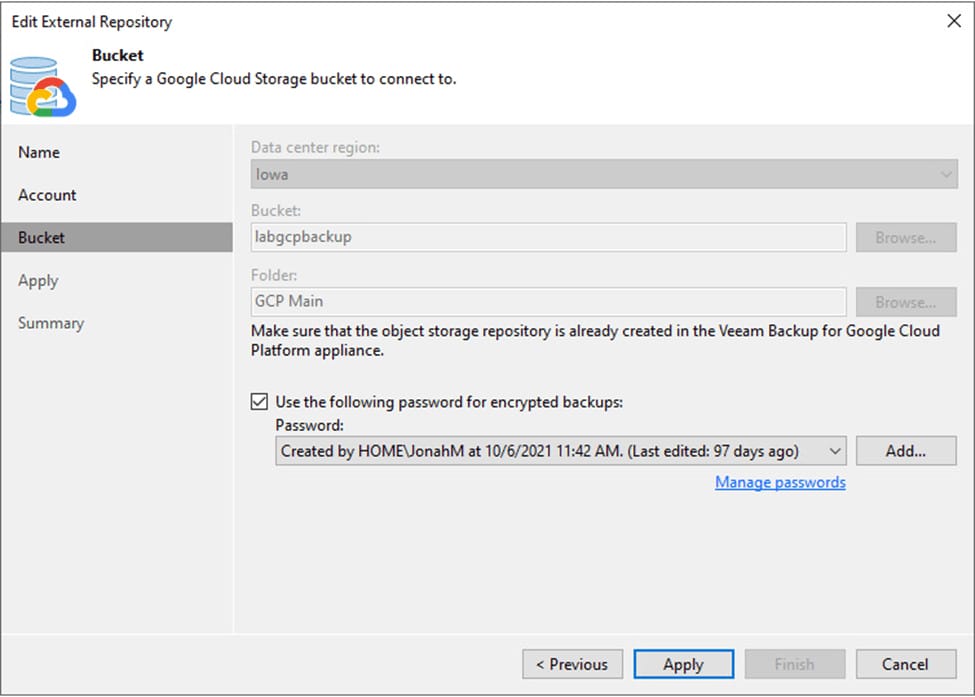
Next, select the data region, select or create a bucket, and select or create a folder. This is also the time to set an encryption password for the repository if you wish to have one. Then, apply and save the settings.
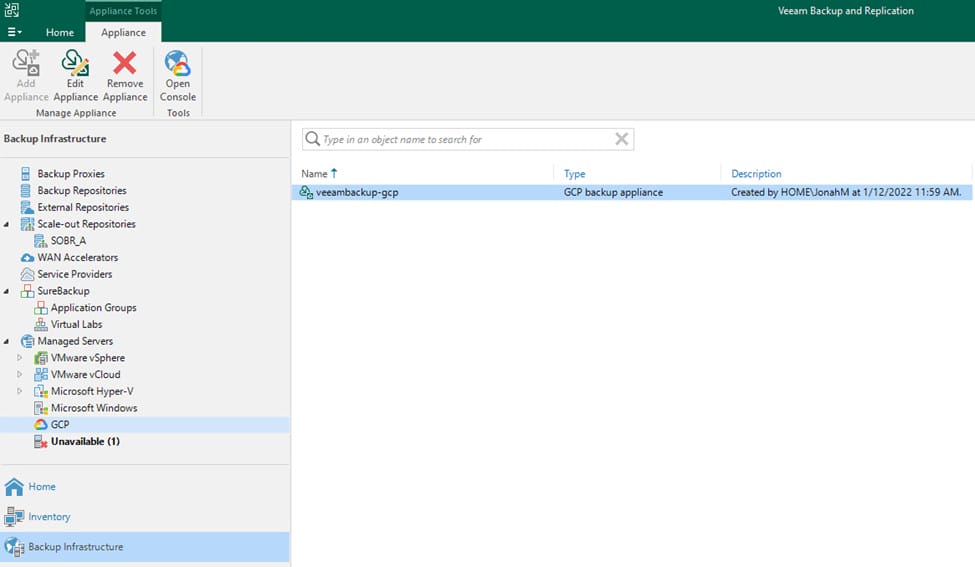
Before we can begin defining backup policies, we will also need to create at least one worker instance. To do this, we will need to launch the appliance’s web UI, which can be done under the Managed Servers menu.
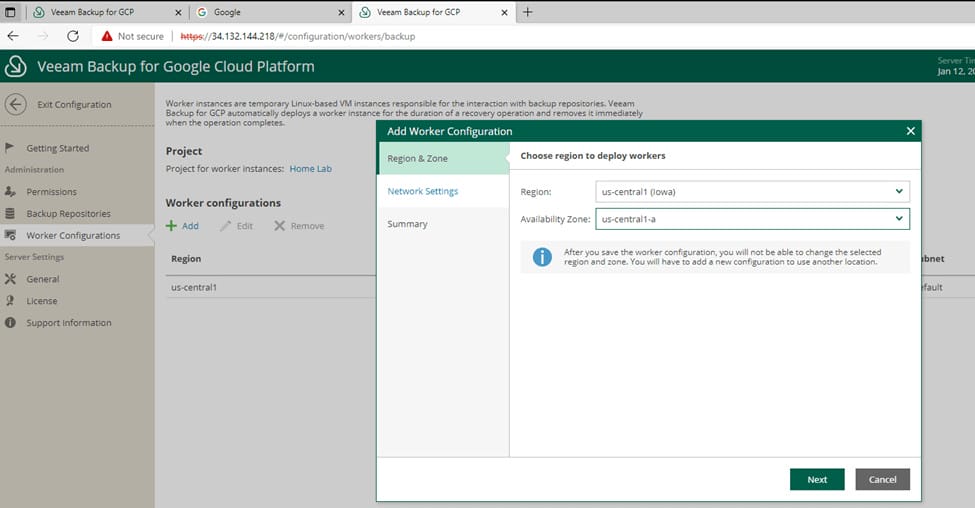
Click Configuration on the top right, then select Worker configurations from the left-hand menu. Use the Add button to begin worker creation. Specify the deployment region and availability zone.
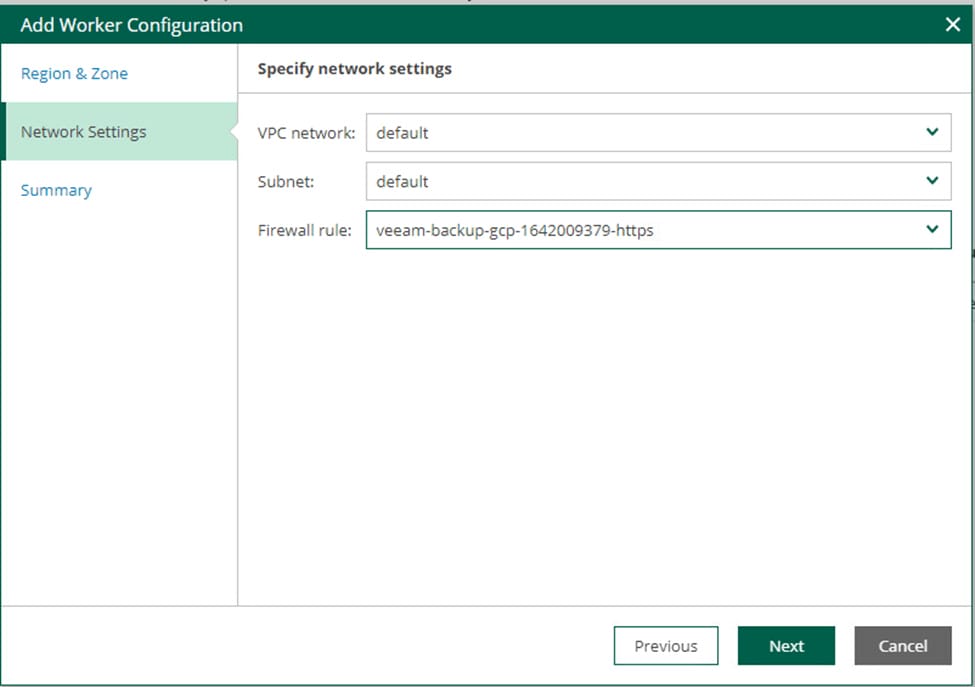
Next set the VPN network and subnet. Make sure to select a subnet that has Google Private Access enabled. Then select a firewall rule that allows HTTPS traffic. You will be presented with warnings on this screen if you have selected a subnet without Google Private Access or a firewall rule without HTTPS access.
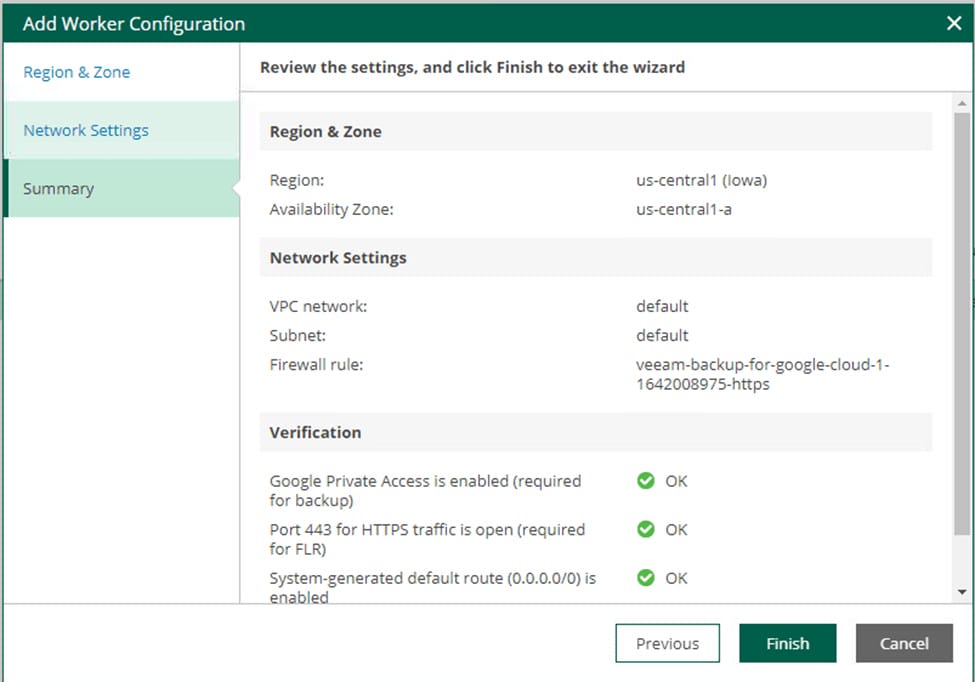
Confirm your settings, check for any warnings, and click Finish to save the worker configuration.
Backup Policy Configuration
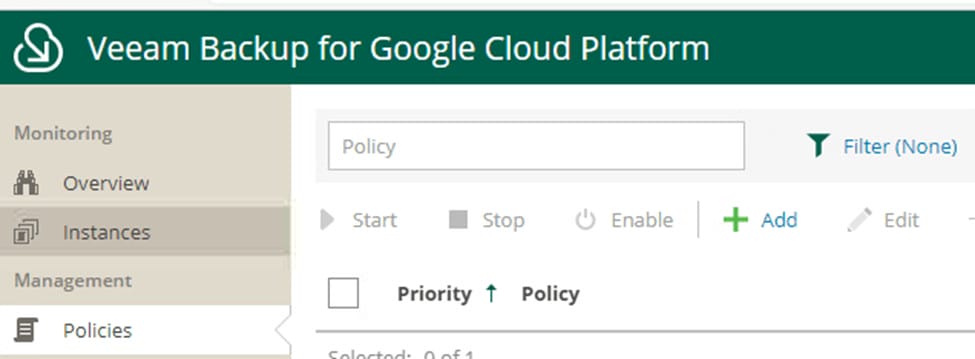
Now we are ready to begin configuring backup policies. Exit the appliance configuration and select Policies from the left-hand menu. Click Add to begin setting up the first backup policy.
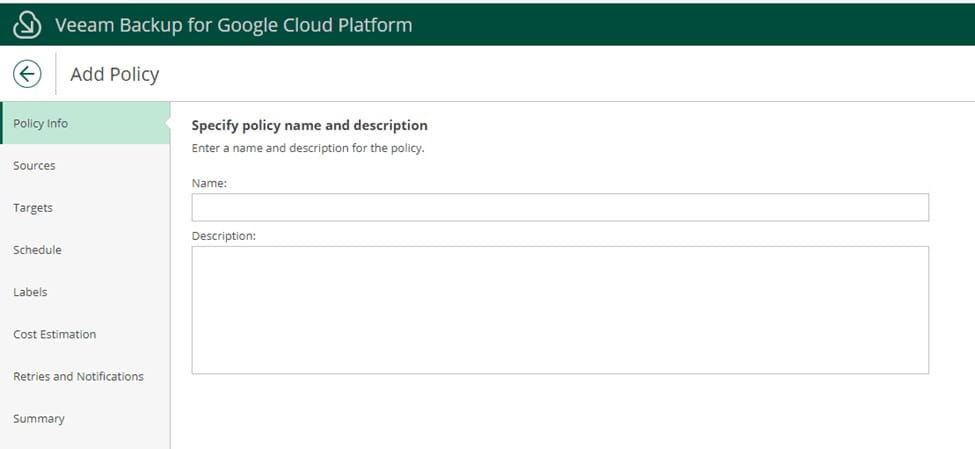
Start by giving the policy a name and description.
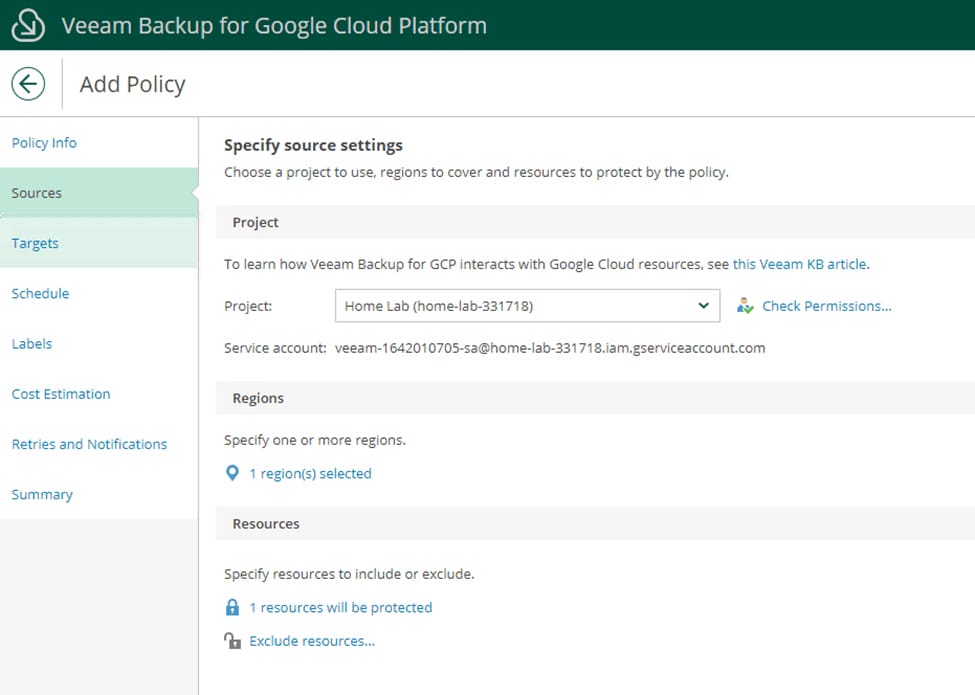
Now double-check the policy to interact with and select the region(s). Finally, choose what resources the policy should protect.
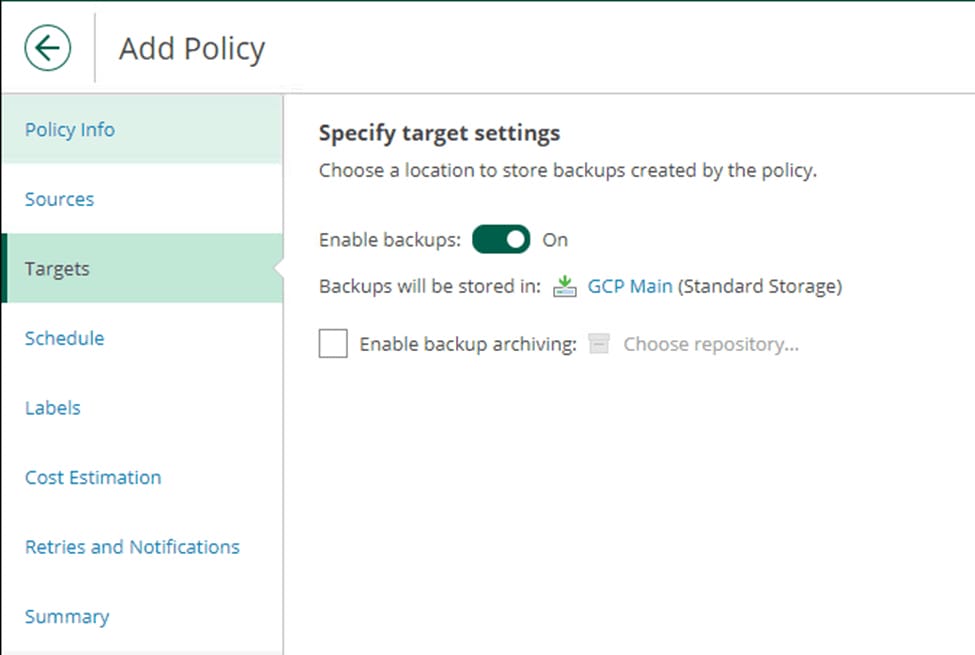
Enable backups and choose the repository created earlier.
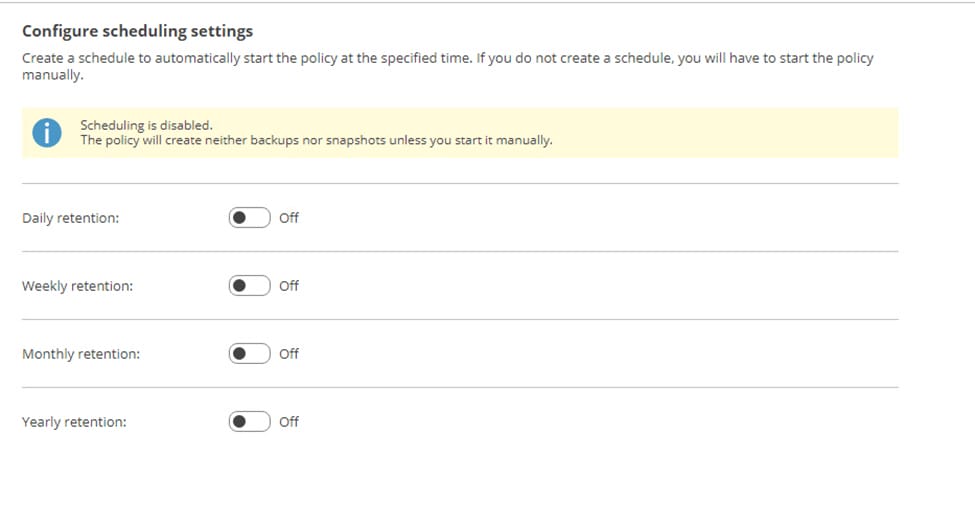
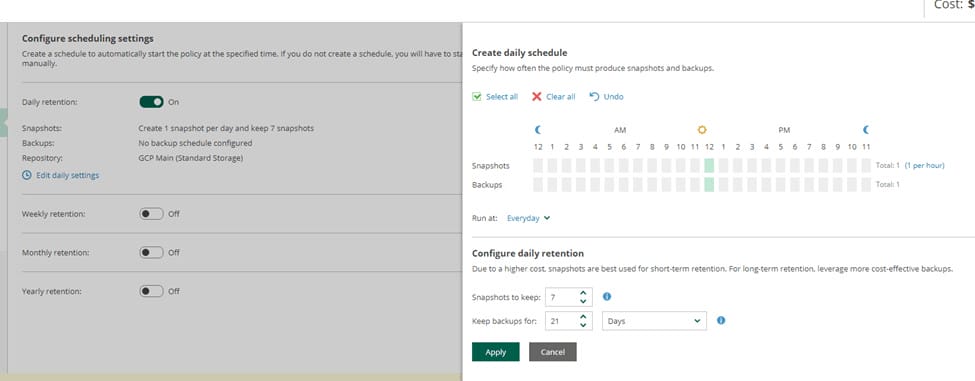
Next retention is configured for backups and snapshots.
For each type of retention you wish to process, turn the retention on and edit the settings. Under the retention’s settings, you can set run schedules and retention periods.
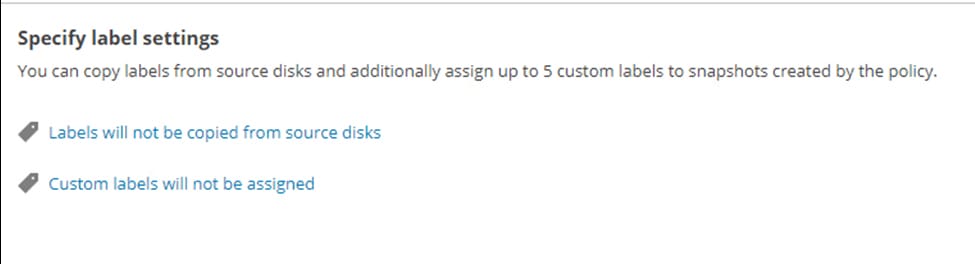
After the policy schedule, you can set whether to save resources labels in the backups and whether to create custom labels on the resources.
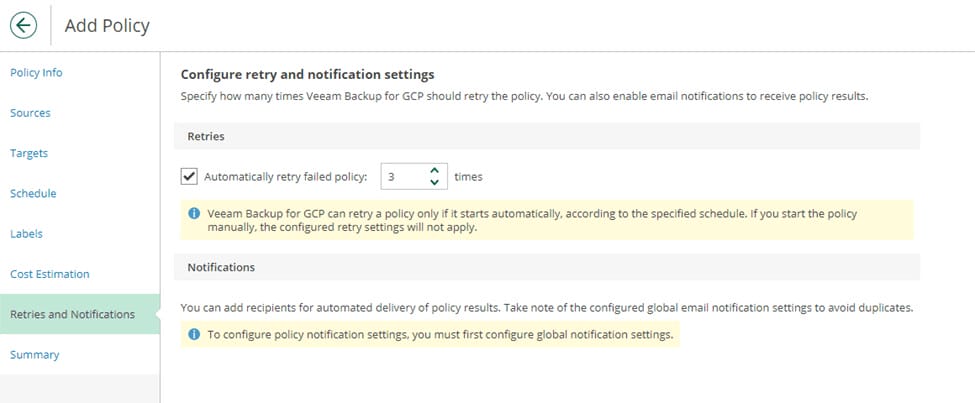
After a cost estimation for the policy, you can configure retry and notification settings, then save the policy.
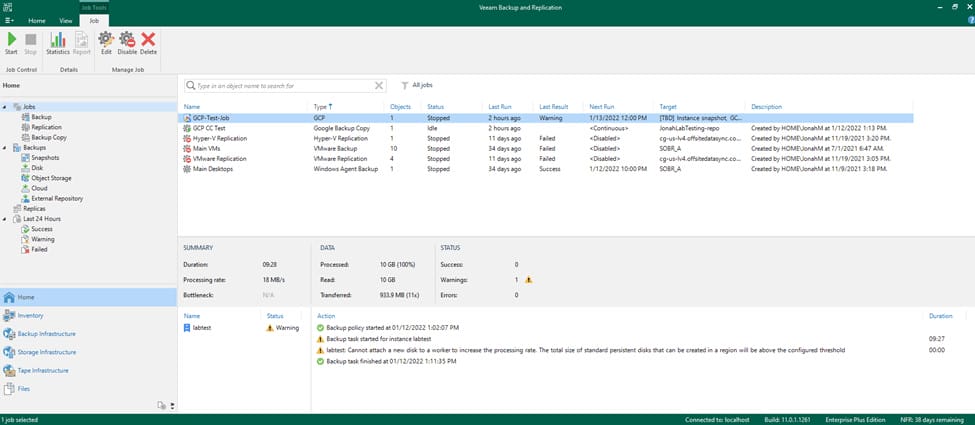
Back in the VBR console, you will now be able to see the backup policy under the Home screen’s Jobs menu. From the VBR console, you are able to start, stop, and disable the backup policy, as well as view session history.
Creating Backup Copy Jobs
From the VBR console, you are also able to create backup copy jobs of GCP backup policies. These backup copy jobs can be configured to point to regular backup repositories and to Veeam Cloud Service Provider (VCSP) repositories, meaning your GCP resources can be granted the same offsite protection as your on-premises workloads.
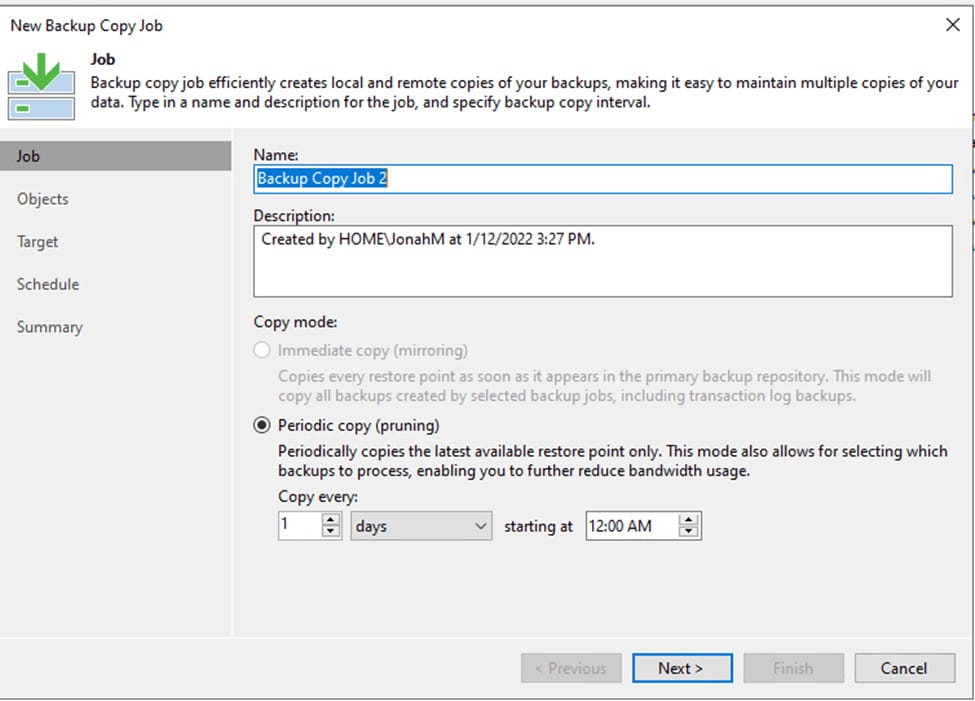
The process for configuring these backup copies is nearly identical to backup copies for virtual machines and agents. However, when creating a backup copy job, there is a new GCE backup option.
The only notable difference is that you can only select Periodic Copy (pruning) mode for the copy job.
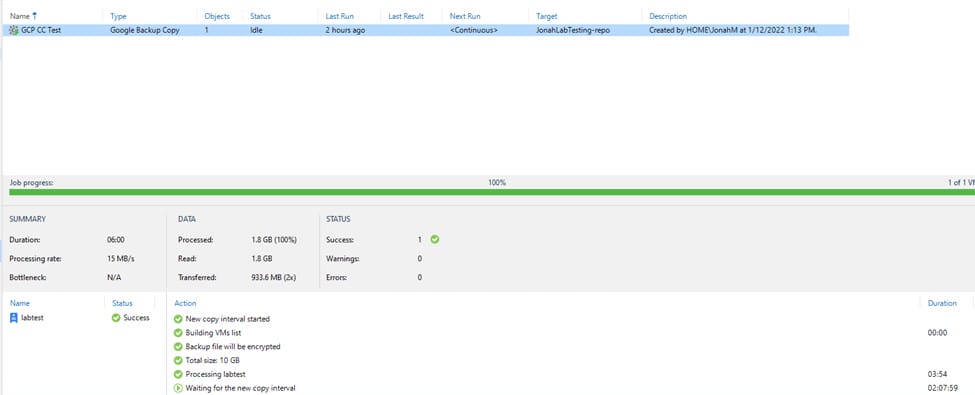
Here is an example of a GCP backup copy, pointed to one of Cyber Fortress’ Veeam Cloud Connect servers in their Las Vegas data center.
In an emergency, Cyber Fortress would be able to use this backup to restore my workload back to GCP or recover it to a hypervisor in their data center until restoring back to my GCP environment is possible. See also
Veeam Backup for AWS wiith VBR.